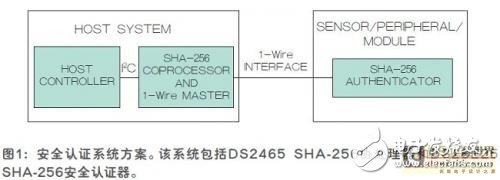
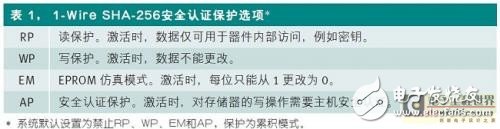
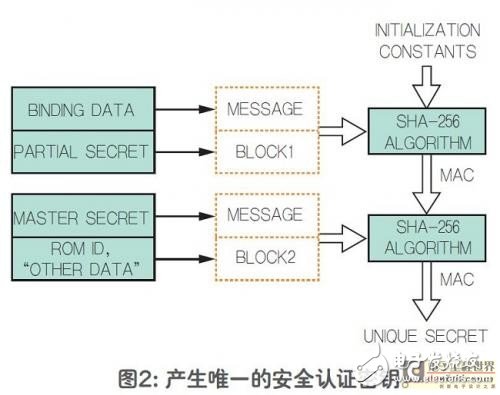
In the last decade, SHA-1 security certification has been an effective weapon for anti-counterfeiting and preventing illegal theft of intellectual property. With the advancement of computer technology, users need to obtain a higher level of security solutions. Based on this demand, Maxim Integrated introduced a new set of SHA-256 security authenticators and supporting security coprocessors. This family of products offers advanced physical security for unmatched low-cost IP protection, cloning and peripheral security certification. This article describes the working principle based on SHA-256 security authentication and the two-way authentication function adopted by the security authentication system. Implementing a secure authentication system requires a sensor/peripheral module to connect to the host system. The system shown in Figure 1 consists of a 1-Wire SHA-256 secure authenticator and a SHA-256 coprocessor with 1-Wire master functionality. The work between the host and peripherals is achieved through a single pin on the 1-Wire interface, reducing interconnect complexity, simplifying design, and reducing cost. The system's SHA-256 security authentication supports 256-bit challenge with a 256-bit key. The security authenticator shown in Figure 1 is a 1-Wire slave with a unique 64-bit ROMID as the basic data unit for secure authentication calculations. The system designer can divide the EEPROM of the authenticator into a publicly accessible (unprotected) area and an area that the host must securely authenticate itself to. Table 1 shows the available protection modes and combinations of protection measures. SHA-256 coprocessor with built-in 1-Wire host The SHA-256 coprocessor in Figure 1 is an I2C slave controlled by the host processor. From the host's I2C port, the SHA-256 coprocessor is a 256-byte read/write memory, and specific areas (data sources) are assigned for special purposes. Safety logic SHA-based security relies on a message authentication code (MAC) computed from public data and keys. To ensure secure authentication, both sides (ie host or coprocessor and 1-Wire security authenticator) must know the "never leak" key. In addition, for maximum security, the keys in each 1-Wire Secure Authenticator must be unique. In this way, once a security authenticator's key is compromised, the security of the entire system is not affected. At first glance, there seems to be no way to achieve these goals. But we have adopted a simple solution, which is to use some "data source" to calculate the key and then install it inside the device in a trusted/controlled production environment. The data source used to calculate the secure authentication key includes: master key, binding data, sub-key, ROM ID of the security authenticator, and filler/formatted symbols ("other data"). The process is shown in Figure 2. Show. Although the data source is public at some point in time, such as in a trusted production environment, the calculated key is never exposed and is always hidden. For security and storage considerations, the unique keys of all secure authenticators in the system cannot be stored in the coprocessor or host; the coprocessor stores the master key and binding data only in the protected memory portion. The split key is a system constant that can be encoded and publicly exchanged in the firmware of the host processor. After reading the ROMID of the secure authenticator, the coprocessor can calculate the unique key of the secure authenticator, as shown in Figure 2. The secure authenticator and coprocessor then share a unique secure authentication key and the system can work. Crystal Clear Back Sticker,Phone Sticker,Mobile Phone Back Skin,Crystal Clear Phone Skin Shenzhen Jianjiantong Technology Co., Ltd. , https://www.jjtphonesticker.com