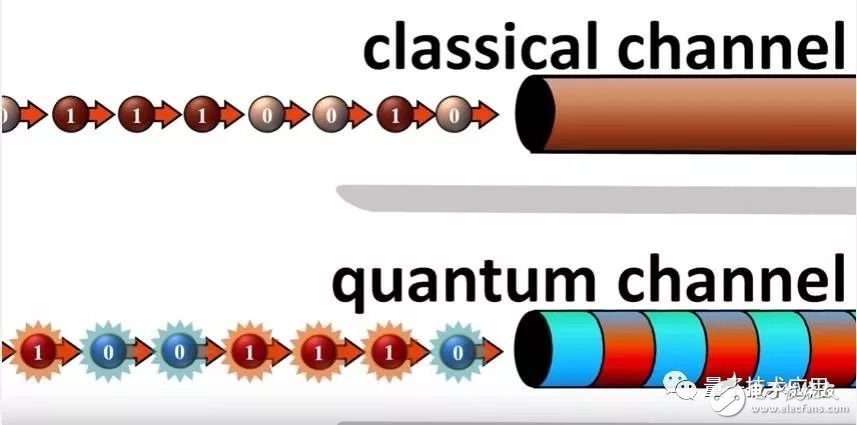
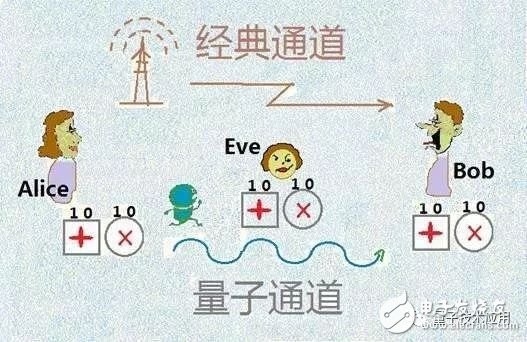
At present, cyberattacks are growing rapidly, threatening and hindering the transformation of various industries into the digital world. As a new interdisciplinary subject developed in the past two decades, quantum communication technology has gradually moved from theory to experiment and to practical development. And its many security attributes are becoming an important means of defending China's high-level security communications. The most widely used public key cryptosystem is the RSA system, and its security is based on the computational complexity of "majority factorization." In theory, if you want to factor a 300-bit Arabic number, it takes about 150,000 years to use a trillion-dollar classic computer. In the future, with the development of quantum computing technology, according to the theory of Shor quantum algorithm, the use of Wanhua's quantum computer takes only 1 second, which will also lead to the RSA public key cryptosystem in the ultra-fast computing of quantum computers. Unbearable. At present, cyberattacks are growing rapidly, threatening and hindering the transformation of various industries into the digital world. As a new interdisciplinary subject developed in the past two decades, quantum communication technology has gradually moved from theory to experiment and to practical development. And its many security attributes are becoming an important means of defending China's high-level security communications. (Photo: from the network) Traditional encryption can be cracked After years of development, information technology is facing two serious challenges. First of all, it is the problem of information security bottlenecks. Since all traditional encryption algorithms that rely on computational complexity may be cracked in principle, they have become a major bottleneck in communication technology. (Photo: from the network) Traditional encryption algorithms may be cracked in principle. The widely used RSA 512-bit encryption algorithm has been cracked in 1999. RSA 768 was cracked in 2009, RSA 1024 bit? That is to say, with the development of computing power, the original secure encryption algorithm may become unsafe. Unable to complete 2 80 searches/years Second, the computing power at this stage is very limited. Because the traditional computing power development model based on Moore's Law is showing serious constraints. Even some scientists have exemplified that even if all the computing power in the world, including people's mobile phones, is added up, the sum of global computing power can't currently complete 2 80- or 90-degree data exhaustive search in one year. . (Photo: from the network) So far, classical encryption techniques are mostly based on the computational complexity of specific mathematical problems, and in theory can not guarantee absolute security. The computing power at this stage is very limited, and the above bottleneck problem has obviously brought an immeasurable threat to the current communication security. Quantum: It is a very small particle. It is the most basic unit of matter and the most basic carrier of energy. It has an indivisibility. The quantum non-cloning theorem leads to the inability of quantum to be accurately copied. It is for this reason that it cannot replicate the quantum by measurement, which constitutes a prerequisite for the security of quantum cryptography. Based on the basic principles of quantum mechanics of "quantum indivisibility" and "quantum non-cloning theorem", quantum cryptography provides us with a new cryptographic solution. Figure: Classic channel and quantum channel (from the network) In 1984, Bennett of IBM and Brassard of the University of Montreal proposed the first Quantum Key DistribuTIon (QKD) solution, the BB84 protocol. The BB84 protocol is by far the most widely used QKD protocol, which solves the problem of secure distribution of keys by encoding the information in the polarization state (phase state) of a single photon, thus avoiding the possibility of information being eavesdropped. Combined with the One TIme Pad (OTP) algorithm invented by Vemam in 1918, it can guarantee the unbreakableness of encrypted content and theoretically realize absolutely secure confidential communication. On the basis of this development, a process of information encoding, signal transmission and other processes based on quantum state communication is also known as quantum communication. Figure: Quantum key distribution (from the network) Quantum communication refers to a new type of communication method that uses quantum entanglement effect for information transmission. It is the only absolute security that has been proved by rigorous mathematics so far. Its core is distributed by quantum key, which realizes the absolute safety of the distant communication parties. Caviar key. Therefore, the history of the development of quantum key distribution is almost the history of the development of lining communication. Caviar key distribution requires information to be encoded in the quantum state of a single photon, but in actual QKD experiments, since the ideal single-photon source technique is not yet mature, a weak coherent light source is often used instead, which also results in a subkey. Distribution has the potential to be attacked by Photon Number Split TIng (PNS). In response to this problem, Hwang of Northwestern University in the United States proposed a deceptive idea that was widely used in 2003. Then in 2005, Professor Wang Xiangbin from Tsinghua University and Lo from the University of Toronto independently proposed a practical decoy scheme, which greatly improved the theoretical safe transmission distance of quantum key distribution based on weak coherent light sources. With the introduction of the BB84 protocol and the decoy theory, quantum communication has developed rapidly and gradually entered the stage of practical use. Its absolute safety based on the fundamental principles of quantum mechanics has made scientists committed to the study of global quantum security networks. Progress in Optical Fiber Quantum With the support of the more mature classic optical fiber communication technology, the development of quantum communication based on optical fiber is particularly skillful. In 1993, Muller et al. of the Gisin team at the University of Geneva completed the experimental verification of fiber-optic quantum key distribution based on polarization coding for the first time, transmitting distance lkm, and then increased this distance to 23 km in 1995. In 2004, Gobby et al. of Cambridge University refreshed the transmission distance of fiber quantum key distribution to 122 km. However, as of 2005, there were security vulnerabilities in these early experiments because PNS attacks against weakly coherent light sources were not considered. After the decoy theory was put forward, in 2007, Peng Chengzhi and others from the Pan Jianwei Group of the University of Science and Technology of China and Rosenberg of the Hughes Group of the Los Alamos National Laboratory in the United States completed the decoy quantum key distribution of more than 100 km of fiber transmission distance. experiment. In 2010, Liu Yang and others from the Pan Jianwei team realized a 200 km fiber quantum key distribution experiment. In 2015, Korzh et al. of the Gisin team updated the transmission distance to 307 km, which is the maximum transmission distance of the current Fibre Channel. Figure: Quantum-secured communication Beijing-Shanghai trunk line (from the network) On the other hand, with the success of optical fiber quantum communication technology, practical fiber-optic quantum communication networks have gradually developed, including the DARPA quantum communication network in the United States, the SECOQC quantum communication network in Europe, the SwissQuantum quantum communication network in Switzerland, and Tokyo. The Tokyo Quantum Communication Network and more. The Pan Jianwei team of the University of Science and Technology of China has also established a practical metro quantum communication experiment network in Beijing, Jinan and Hefei, respectively. Combined with the quantum communication "Beijing-Shanghai trunk line" currently under construction, it will connect Beijing, Jinan and Hefei in the future. And Shanghai, to achieve a thousand-kilometer-level business of trusted, scalable wide-area fiber-optic boy communication. Progress in free space quantum communication There is an inherent loss in the transmission of photons in the fiber channel. This loss is typically 0.2 dB/km in the 1550 nm band. At the same time, due to the birefringence effect of the fiber, the coherence of the photons after long-distance transmission becomes poor. The communication distance of quantum communication has gradually reached the bottleneck. Compared to fiber-optic channels, photons have less attenuation in free-space transmission, and there is almost no birefringence in the atmosphere, which makes quantum communication based on free space develop rapidly in recent years. In 1989, Bennett et al. completed the experimental verification of quantum key distribution for the first time on a desktop platform with a communication distance of 32 cm. In 1998, the Hughes team completed a free space quantum key distribution experiment with a transmission distance of 1 km, and in 2002 realized a 10 km daytime free space quantum key distribution experiment. In 2003, Aspelmeyer of the Weilinger team of the University of Vienna completed the unidirectional entanglement photon transmission of 600 m free space for the first time. In 2005, the Pan Jianwei team realized the 13 km bidirectional entanglement photon distribution in Hefei, and verified the feasibility of entangled photons crossing the equivalent atmospheric thickness for the first time in the world. In 2006, Weier et al. of the Weinfurter team completed experimental validation of entangled quantum key distribution. In 2007, the European Joint Laboratory headed by Zeilinger realized a 144 km free-space entangled photon unidirectional transmission experiment and a decoy quantum key distribution experiment, which is the transmission distance of the free-space channel to date. Then in 2009, the team validated the entangled quotient fidelity transmission of the 144 km atmospheric loss free-space channel. In 2012, Pan Jianwei team realized a 101 km free-space quantum entanglement distribution experiment in Bohai Lake. Figure: 100-kilometer quantum entanglement distribution experiment of Qinghai Lake Lake Heart Island (from the network) In 2013, the Weinfurter team completed a 20 km free space quantum key distribution experiment based on an aircraft motion platform. In the same year, Pan Jianwei completed a comprehensive demonstration experiment on the distribution of quantum key in Xinghai Lake in Qinghai Lake, paving the way for Xingdi Quantum Communication and the global caviar security network. In January 2018, Professor Pan Jianwei and his colleague Peng Chengzhi and other research teams, together with the Wang Jianyu Research Group of the Shanghai Institute of Technical Physics of the Chinese Academy of Sciences, the National Astronomical Observatory, etc., cooperated with the Austrian Academy of Sciences Anton Zeilinger research group to use the "Mozi" quantum. The scientific experimental satellite, for the first time between China and Austria, realizes the intercontinental quantum key distribution with a distance of 7,600 kilometers, and uses the shared key to realize encrypted data transmission and video communication. This achievement indicates that the "Mozi No." has the ability to realize intercontinental quantum security communication and lays a solid foundation for the future construction of a global quantum communication network. Figure: Schematic diagram of the intercontinental quantum secure communication network (from the network) Pan Jianwei, an academician of the Chinese Academy of Sciences and executive vice president of the University of Science and Technology of China, once said, "I hope that through 10-15 years of hard work, through a rigorous demonstration, a secure communication network system that can communicate wirelessly with the classic network, strengthen network security and communication security. , data authentication and authentication security. At the same time such a network itself can be used to construct a new high-precision global frequency standard delivery." Quantum mechanics has spawned new information technology. In the course of nearly a hundred years of development, it has already prepared for solving major problems. Quantum communication now provides a secure means of communication. It can be said that quantum computing is a nuclear weapon in peacetime. Because China attaches importance to it earlier, although all countries are in the stage of running and running, as long as China continues to exert its strength, the development prospects are still promising. Mini PC Office
Do you know the reason why Mini PC is becoming more and more welcome nowadays? You will realize that Mini PC windows 11 absolutely should be popular if keep thinking deeply a little more, since not only there are all the functions, performance warranty, various ports, but solve the weight problem people struggle when need to move computer in old time. At this shop, you can see Mini PC office, Mini Gaming PC , j4125 Mini PC, etc. Whatever you need for normal office, design drawing, gaming, education learning or teaching, Telecast alive, daily entertainment,etc. You can always find right one here.
Of course, China All In One Business Computer, Education Laptop, Budget Business Laptop, Gaming Laptop , Yoga Laptop , Android Tablet also available at this store, since what we do is customizing Quad Core Laptop, 10.1 android tablet, PC Mini Intel and Business All In One Computer.
Another reason why more and more clients return to us is that quality with competitive price, in time and lifetime after-sales service, customized and multiple service, fast delivery time.
Home Assistant Mini PC,Custom Mini PC,Windows 11 Mini PC,j4125 Mini PC Henan Shuyi Electronics Co., Ltd. , https://www.shuyielectronictech.com